Emu8086 Hardware Interrupt Editor & Generator
If there has been a closed-source software which I have enjoyed using at my university, it’s Emu8086. The shareware, as the name suggests, emulates the 8086 processor down to the minutest detail. Since 8086/8088 processors form a significant part of my Microprocessor Interfacing & Programming course, I have grown rather fond of the software’s workings.
Recently, I needed to generate hardware interrupts on the emulator. Not only that, but I wanted to use my own service routines for the interrupts so that I could try to understand what happens behind-the-scenes in such scenarios. Reading through the Emu8086 documentation, I figured out that two files are responsible for accomplishing the required tasks:
INT_VECT: A 1024-byte interrupt vector containing 256 entries, with each entry being a 4-byteoffset:segmentpair.emu8086.hw: A 256-byte file with each byte representing a corresponding interrupt. A non-zero byte signifies that particular interrupt being active. The byte is set to zero again after the interrupt is serviced.
As manually editing these files became cumbersome, I had to code two PyGTK apps for editing these files in a pretty interface:
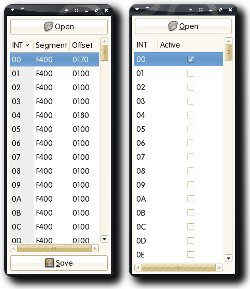
(Click on the thumbnail for larger version.)
The intvecteditor.py file lets the user load/edit/save an 8086 interrupt vector. Similarly, the hwintgen.py allows the user to load an emu8086.hw and then generate/monitor interrupts in it. The utilities require PyGTK to run, but I find it infinitely easier now to analyze interrupt behavior of the emulator. This also lead to an interesting observation, as the emulator checked for interrupts at the beginning of an instruction instead of at its end — something which didn’t confirm with the actual 8086 working model.
x86 is fun. After all,
Tags: 8086, 8088, Assembly, Code, Emu8086, Emu8086 Hardware Interrupt Editor & Generator, Intel, Interrupt, Open Source, PyGTK, Python, Vector, x86“Do you program in assembly?”
“NOP”